Services für Secure Identity and Access Governance aus einer Hand
Die digitale Transformation der Geschäftswelt bietet Unternehmen aller Größen und Branchen vielfältige Marktchancen und Wettbewerbsvorteile. Allerdings entstehen dadurch auch zusätzliche Sicherheitsrisiken. Wer auch in Zukunft wettbewerbsfähig bleiben will, muss daher seine IT- und Geschäftsrisiken auf ein Minimum reduzieren.
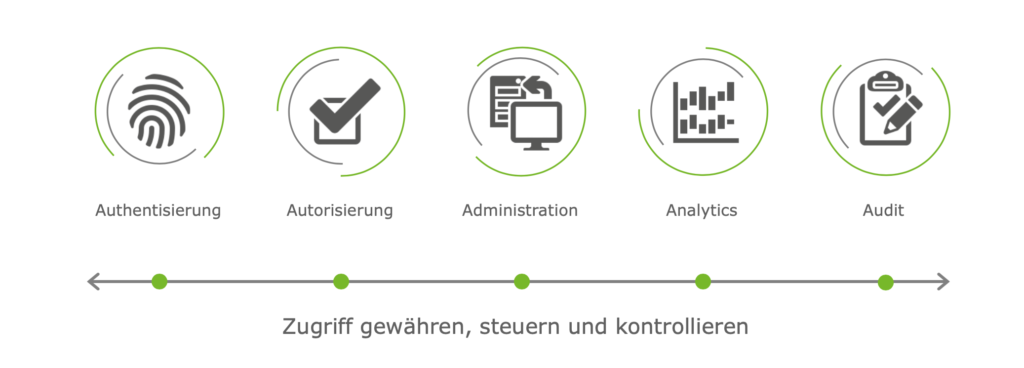
Identity and Access Governance: Von Triple A zu Five A
Das gelingt mit einem ganzheitlichen und an die Kundenbedürfnisse angepasstem Konzept für Secure Identity and Access Governance (IAG) und der Erweiterung des klassischen Triple-A-Prinzips – Authentifizierung, Autorisierung, Administration – durch Analytics (Intelligence) und Audit zum Five-A-Prinzip.
Hier entwickelt KOGIT, mit ihrer langjährigen Beratungs-, Branchen-, Prozess- und Technologiekompetenz, eine individuelle, optimal auf den Kunden abgestimmte IAG-Strategie und setzt diese auf der Grundlage smarter IT-Lösungen um – einfach, schnell, kostenoptimiert und mit umfassenden Services.
KOGIT Services für Identity und Access Management
Die Experten von KOGIT sorgen dafür, dass
Schlanke Lösungen - echter Mehrwert
Damit IAM-Projekte schlank bleiben, ist KOGIT bei den eingesetzten Softwareprodukten bestrebt, die Standardfunktionen einzusetzen und nach Bedarf durch Customizing und/oder eigene Add-Ons und Plugins zu erweitern.
Die enge Zusammenarbeit der KOGIT mit führenden Softwareherstellern garantiert den Kunden Lösungen auf dem neusten Stand der Technik. Durch umfangreiches Branchen-Know-how und exzellente Expertise liefert KOGIT einen großen Mehrwert für die Kunden.